Network Scanning – TCP Flags & TCP 3-Way Handshake
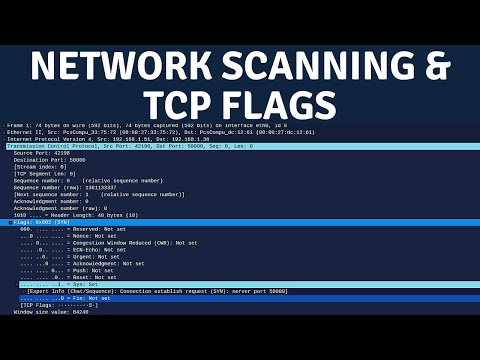
In this video, I explain the importance of network scanning in penetration testing, TCP flags, and the process of the TCP 3-way handshake. Scanning is typically conducted after extensive passive reconnaissance has been conducted on the target. The objective is to identify active targets and potential access vectors in the form of ports and services.
This stage does not involve any exploitation or gaining of access, rather, it is focused on building a profile of the target based on information like OS version, service versions, and any misconfigurations in the stack.
📈 SUPPORT US:
Patreon: https://www.patreon.com/hackersploit
Merchandise: https://teespring.com/en-GB/stores/hackersploitofficial
SOCIAL NETWORKS:
Reddit: https://www.reddit.com/r/HackerSploit/
Twitter: https://twitter.com/HackerSploit
Instagram: https://www.instagram.com/hackersploit/
LinkedIn: https://www.linkedin.com/company/18713892
WHERE YOU CAN FIND US ONLINE:
Blog: https://hsploit.com/
HackerSploit – Open Source Cybersecurity Training: https://hackersploit.org/
HackerSploit Academy: https://www.hackersploit.academy
HackerSploit Discord: https://discord.gg/j3dH7tK
LISTEN TO THE CYBERTALK PODCAST:
Spotify: https://open.spotify.com/show/6j0RhRiofxkt39AskIpwP7
We hope you enjoyed the video and found value in the content. We value your feedback. If you have any questions or suggestions feel free to post them in the comments section or contact us directly via our social platforms.
Thanks for watching!
Благодарю за просмотр!
Kiitos katsomisesta
Danke fürs Zuschauen!
感谢您观看
Merci d’avoir regardé
Obrigado por assistir
دیکھنے کے لیے شکریہ
देखने के लिए धन्यवाद
Grazie per la visione
Gracias por ver
شكرا للمشاهدة
#Nmap#TCP .
Comments are closed.